AWS Identity and Access Management (IAM) is a web service that enables Amazon AWS users to manage users and user permissions. Use of IAM, you can centrally manager users, security credentials such as access keys and permissions that control which AWS resources users can access.
In this blog post you will go through following areas,
- Exploring pre-created users and groups in IAM
- Inspecting IAM policies as applied to the pre-created groups
- Following a real-world scenario, adding users to groups with specific capabilities enable
- Locating and using the IAM Sign-in URL
- Experimenting with affects of policies on service access
Before we start exploring about IAM and features, I will explain little what is IAM and the use of it.
Manage IAM user and their access
You can create users and assign them individual security credential (access keys, passwords and multi -factor authentication devices).
Manage IAM roles and their permission
IAM role is a similar to the user. It is an AWS identity with permission policies that determine what the identity can and cannot do in AWS.
Manage federated users and their permissions
You can enable identity federation to allow existing users in your enterprise to access the AWS management console to call AWS APIs and to access resources, without need to create an IAM user for each identity.
Lets start to get hands dirty!
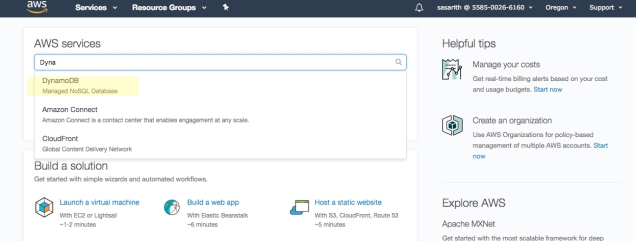
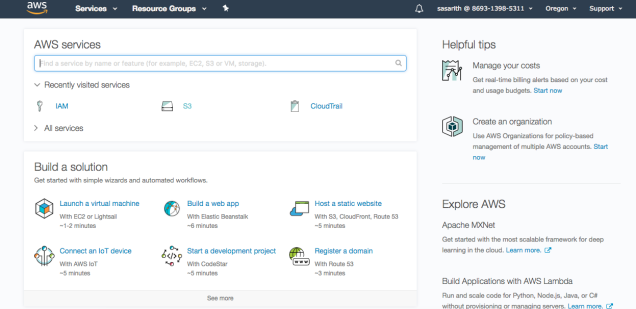
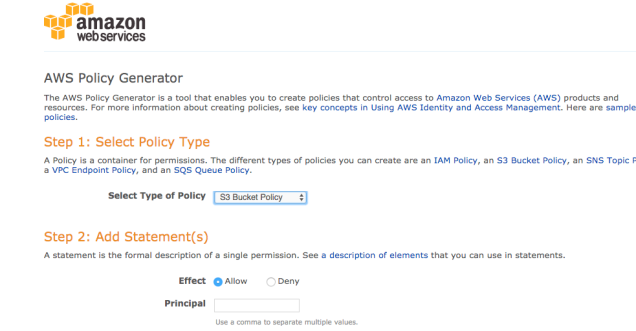
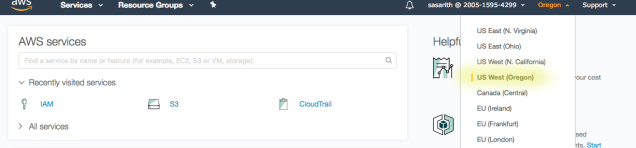
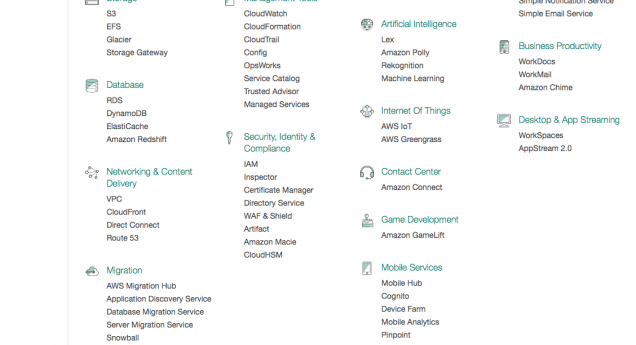
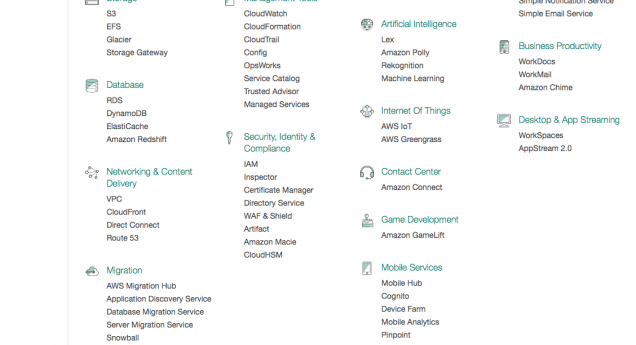
First, log into the AWS console panel using your credential. From there select IAM as shown below.
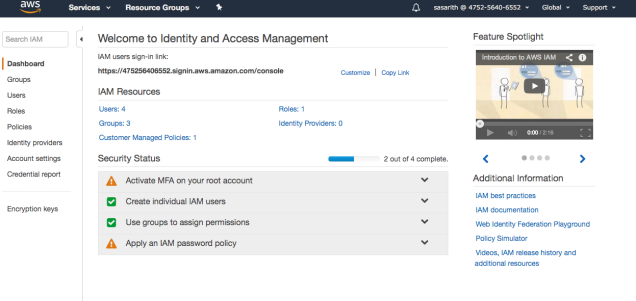
When you entered to the IAM dashboard you will get a window like this
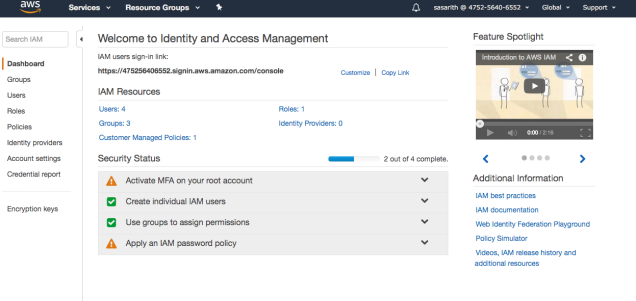
Please note, in my screenshots some of the additional things are added. You might have nothing here. Thats totally okay.
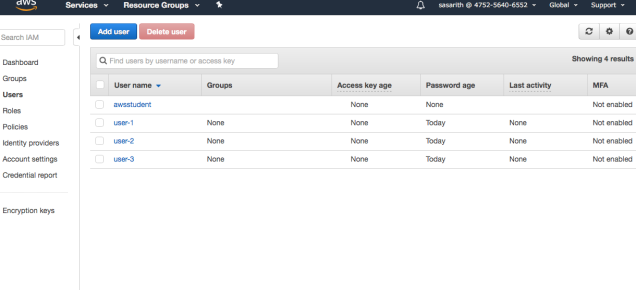
In the left pane you can see ‘Groups’ and ‘Users’. In my users section I have three users that is already created.
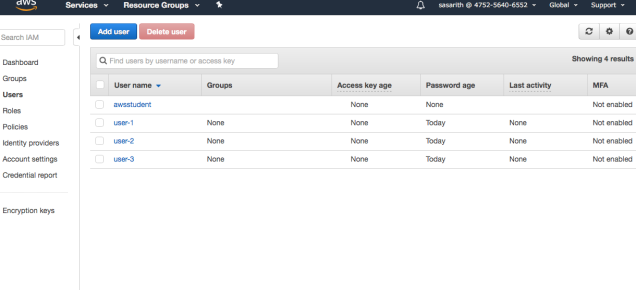
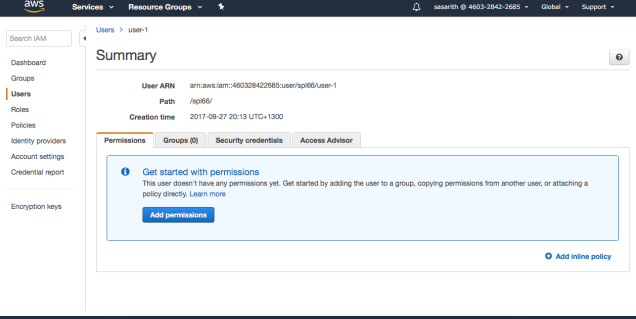
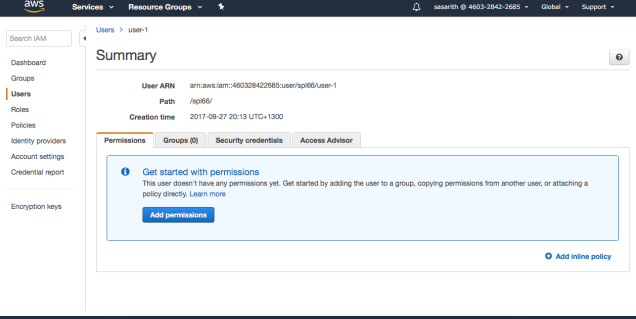
I have just created users and nothing added to users (Permissions or groups)
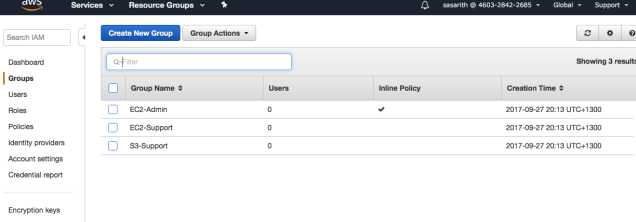
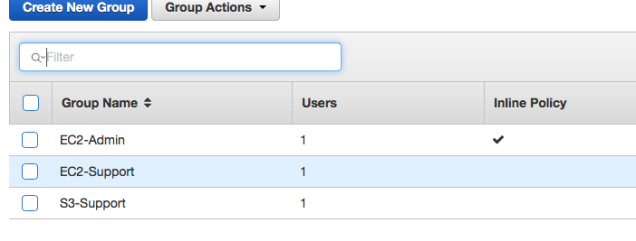
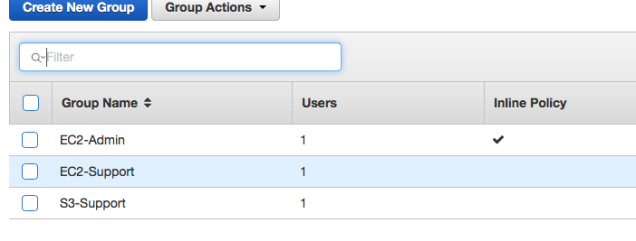
Will check group section now. In the Groups I have three different groups created with three different names. I’ll explain what does these means.
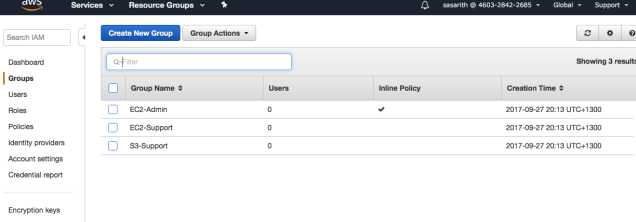
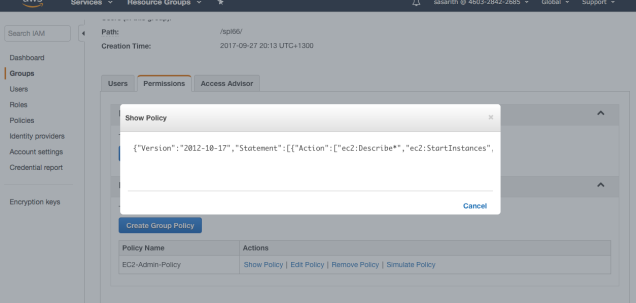
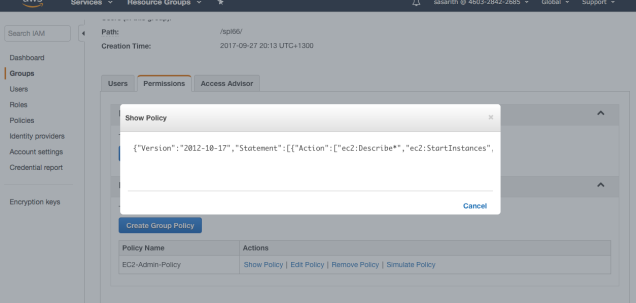
EC2 – Admin
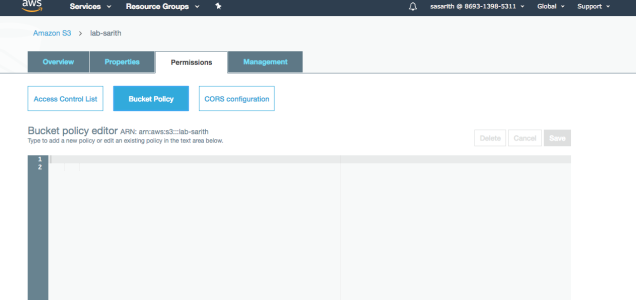
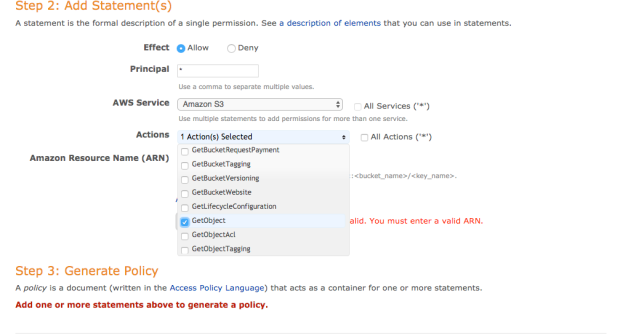
When you clicked a group, there are many options over there. In the policy actions, there is a option to view the policy. Under Action, click Show Policy. So, this is my policy. This policy is a inline policy which is assigned to one user or one group. Inline policies are used to override standard permissions for specific situations
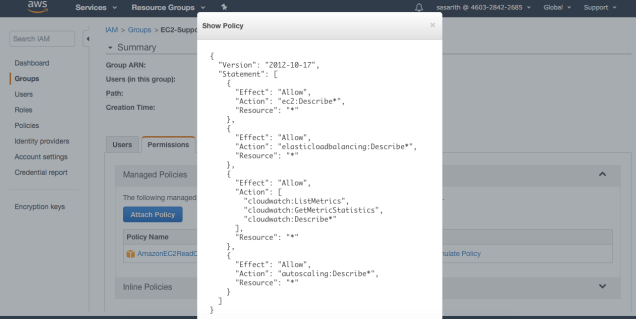
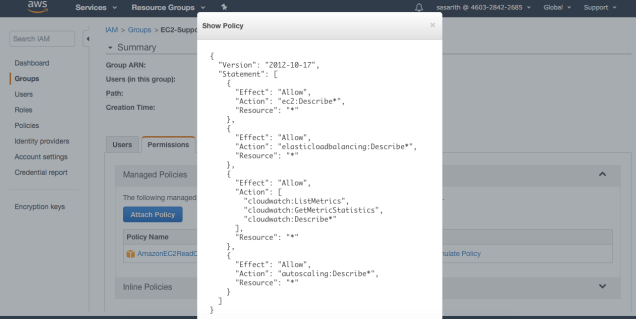
EC2 – Support
I am going to apply the above steps other groups as well. So this is the EC2 – Support policy. What does this mean ?
Policy defines what actions are allowed and what actions are denied for specific AWS resource. This policy granting permission to list and describe information about AWS EC2, Elastic Load Balancing, CloudWatch and Auto Scaling. This is not granting permission to modify.
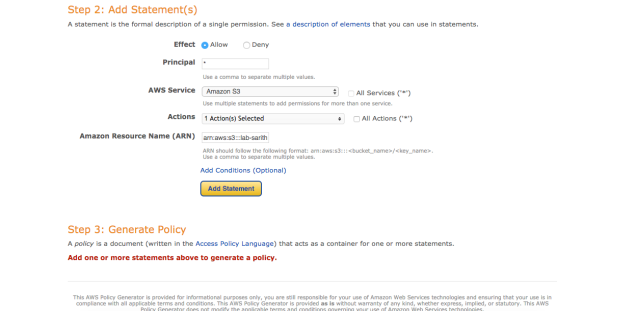
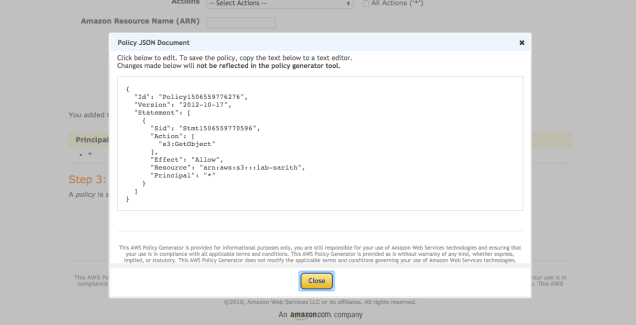
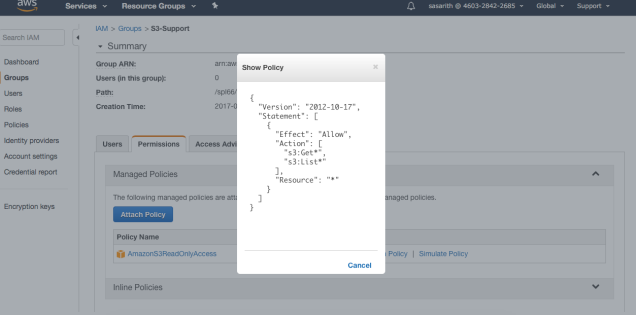
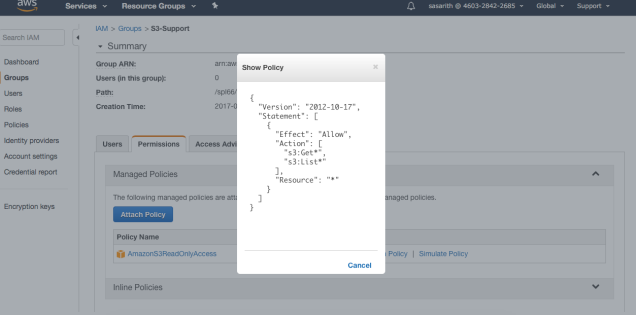
S3 – Support
This is the the policy for the S3 – Support group. This policy giving permission to get and list resources in Amazon S3.
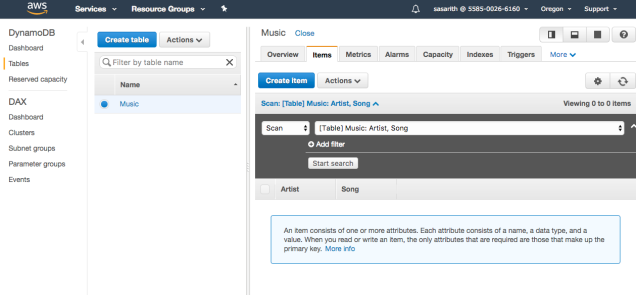
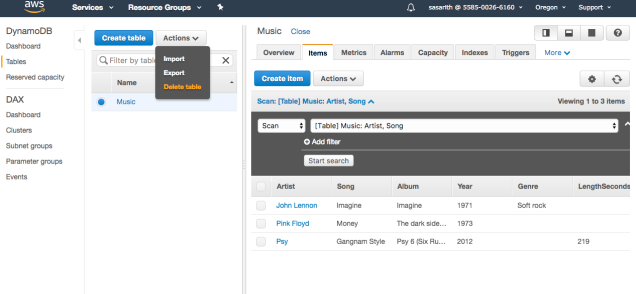
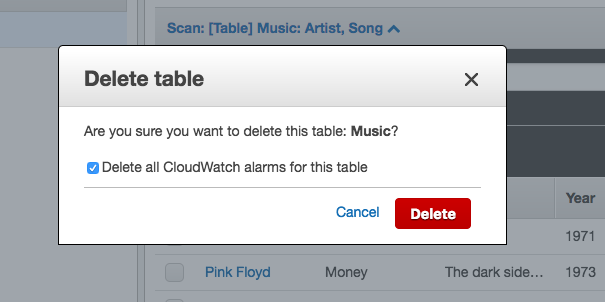
Now will see how we can add these policies to users.
We are going to add users as follows
User-1 –> S3 – Support
User-2 –> EC2 – Support
User-3 –> EC2 – Admin
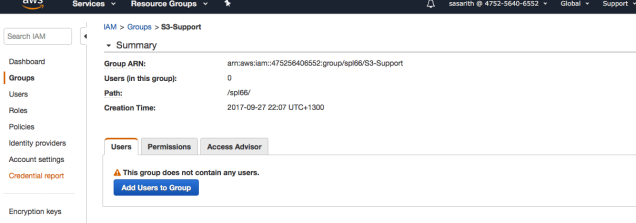
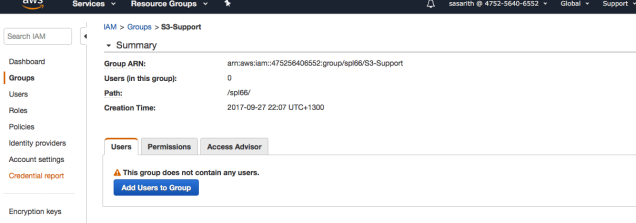
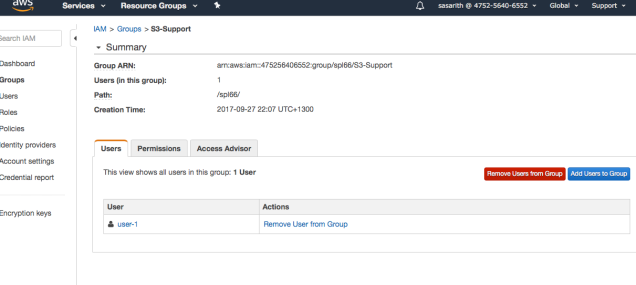
Our first step is adding User-1 to the S3 – Support group.
Click on the S3- Support group. According to my scenario I am getting following window. Click Add Users to Group
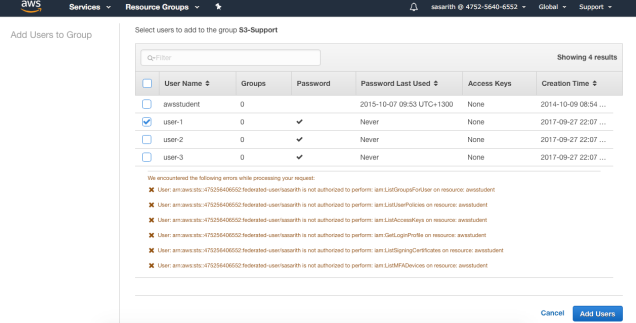
After that step you will get another step to select the user. From there select the user and click add user.
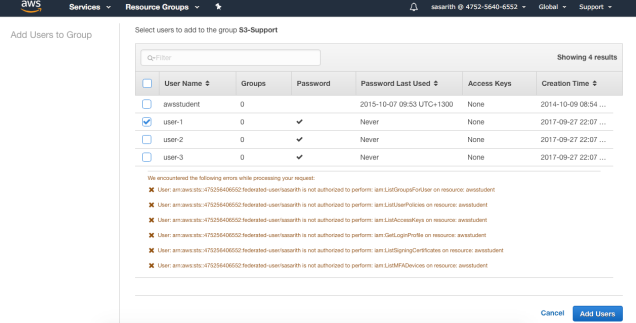
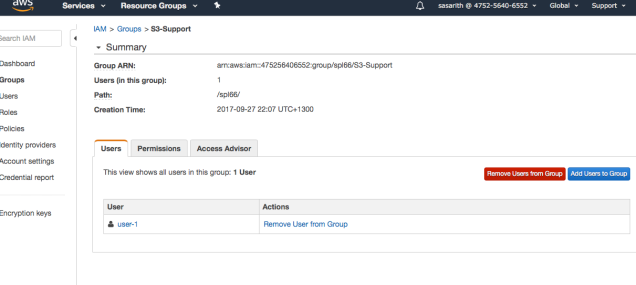
After you added the user and if it is successfully worked then it should be like this.
Likewise, I have added all other two users as well to each groups and you can see now all the groups has one user.
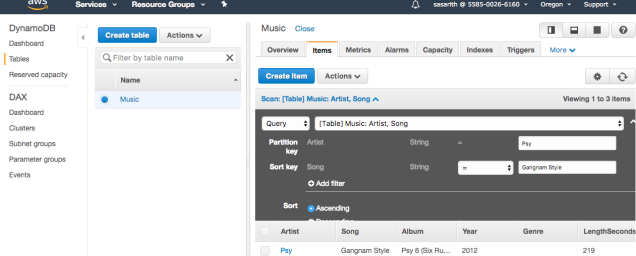
Now we will log on to the Amazon Console and check whether these policies are working fine.
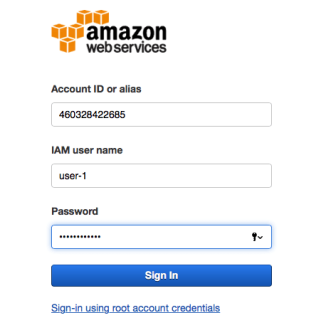
First will look into User-1
Using my IAM user sing-in link I am signing to the console (You can get the link on IAM dashboard) Link is something like this – https://460328422345.signin.aws.amazon.com/console
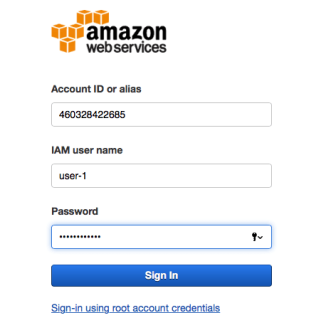
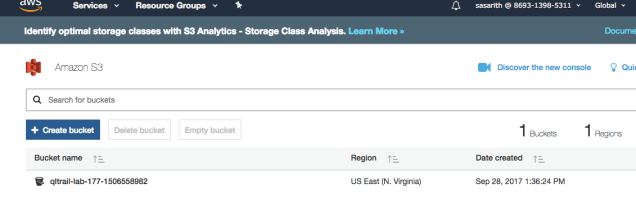
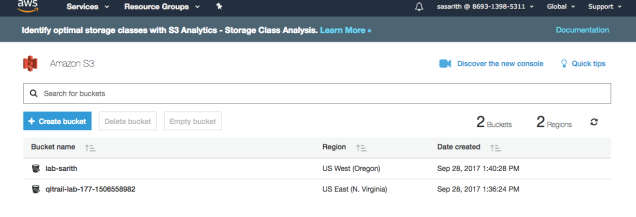
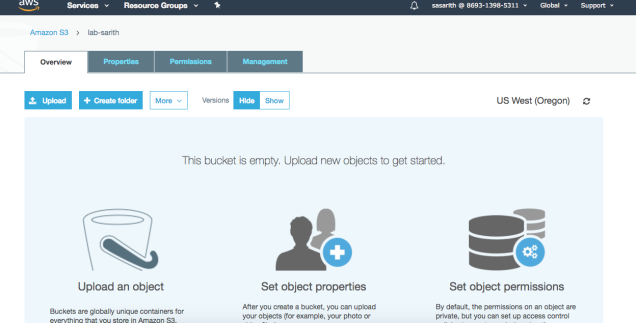
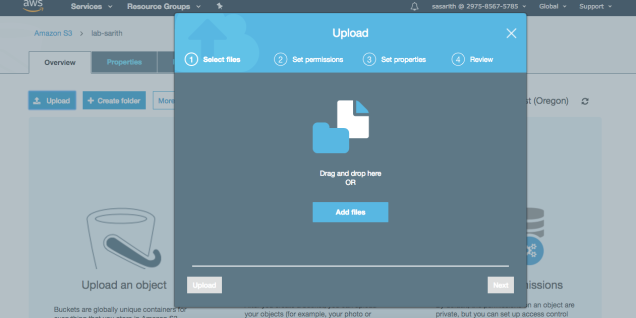
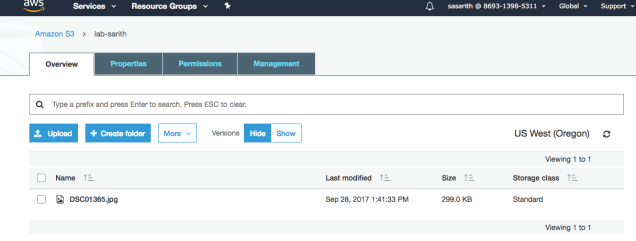
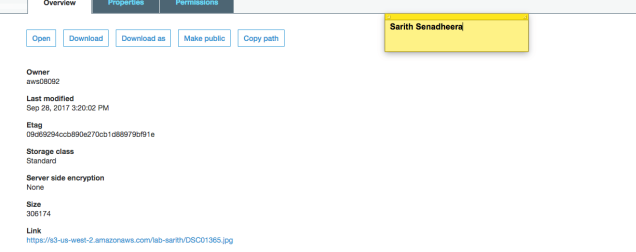
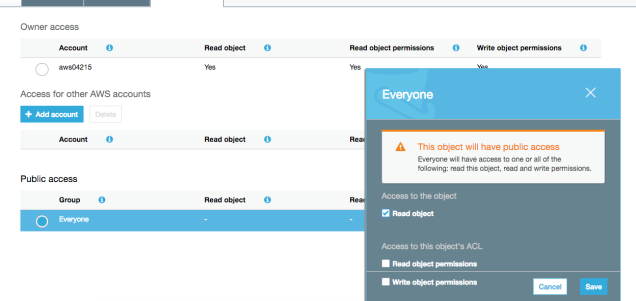
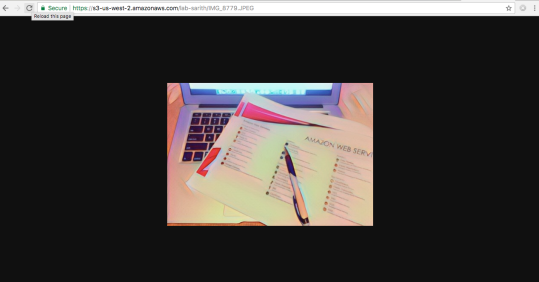
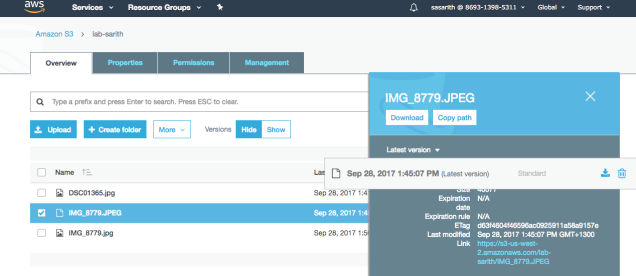
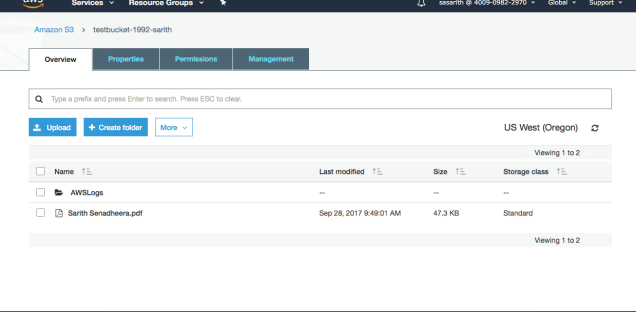
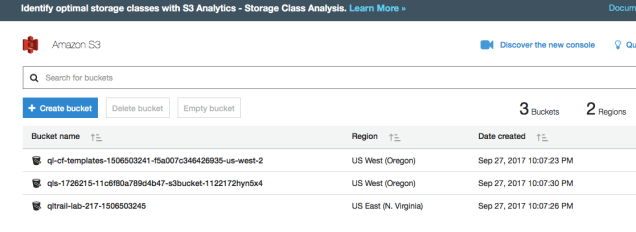
I have entered my credentials to log-in. After I signed in I clicked on S3 service from AWS services menu. Here we are ! I can see my S3 buckets. So lets whether blocked permissions are working.
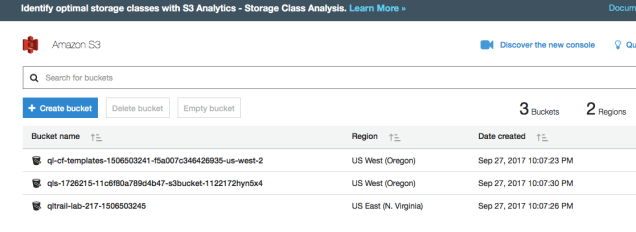
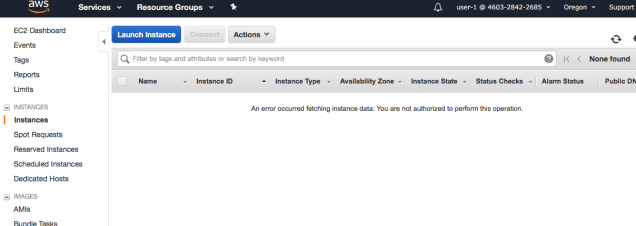
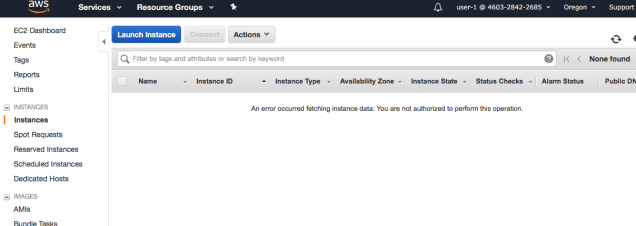
We have blocked accessing EC2 for the User-1 and will see it now. Go to the Services and Click EC2 and from the left pane click Instances. Hurray ! We are getting an error saying “An Error occurred fetching instance data. You are not authorised to perform this operation” That because we have not given permission to the user-1.
Lets see user-2
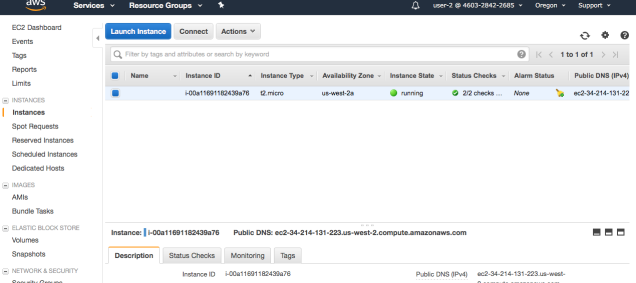
Using the link and the credentials I am logging to the AWS console and then Select the EC2 and Click Instances. Another Hurray ! Its working. User-1 cannot see it but user-2 can.
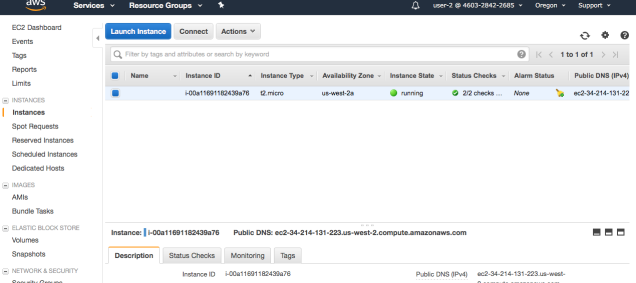
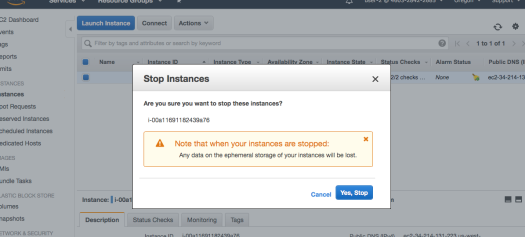
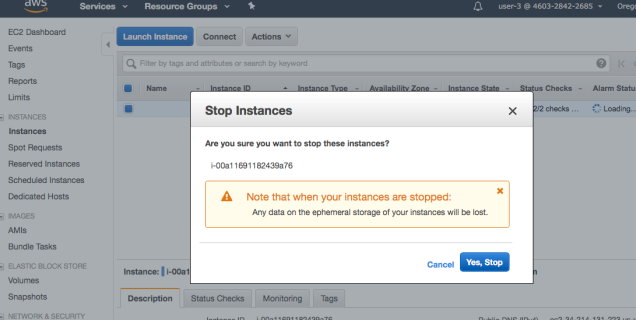
Now click on Actions and will stop the instances and see whether we can perform that operation.
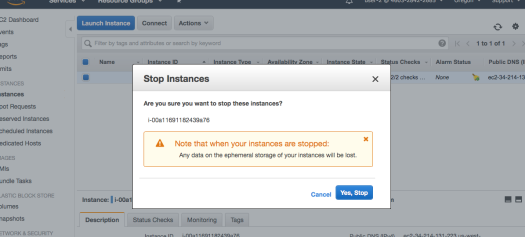
Click Yes,Stop
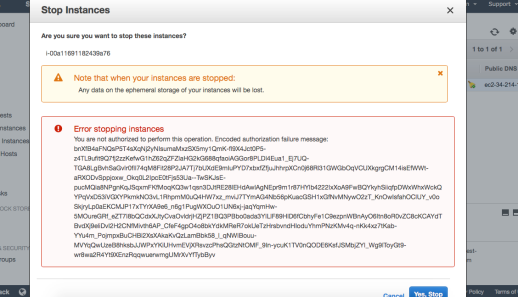
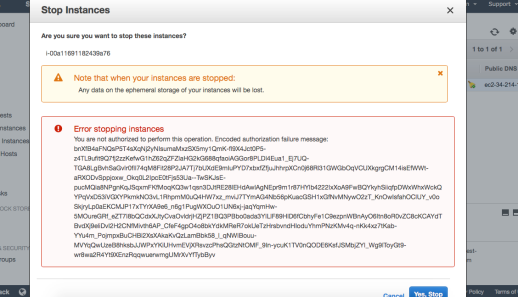 So we are getting the above error after clicked Yes,Stop that because we don’t have admin access to the user-2 but we do have for user-3.
So we are getting the above error after clicked Yes,Stop that because we don’t have admin access to the user-2 but we do have for user-3.
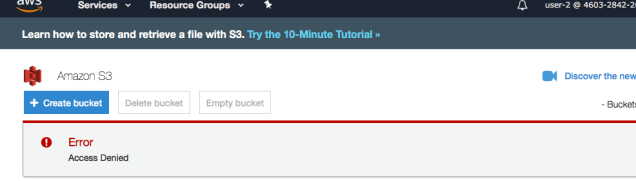
And I will show what we will see when we try to access S3 service. Go to the S3 service from Service menu.
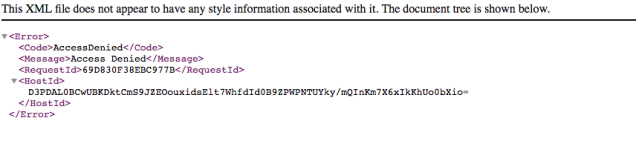
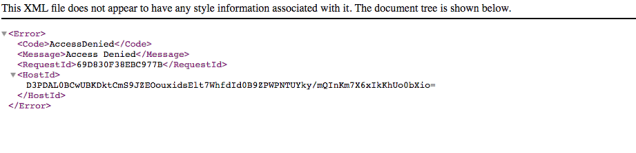
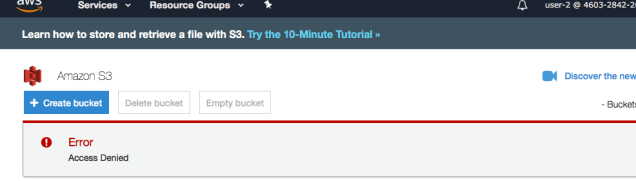 Yes, Its not allowing to access the S3 service because no permissions.
Yes, Its not allowing to access the S3 service because no permissions.
Lets checkout User-3
User-3
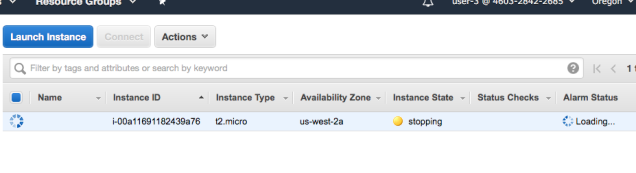
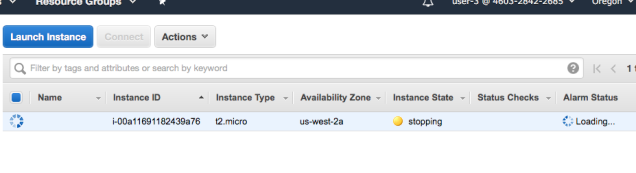
Like earlier times, follow the same steps and log into the AWS console. Then click on Service –> EC2 –> Instances.
After that Click Actions –> Instance State –> Stop
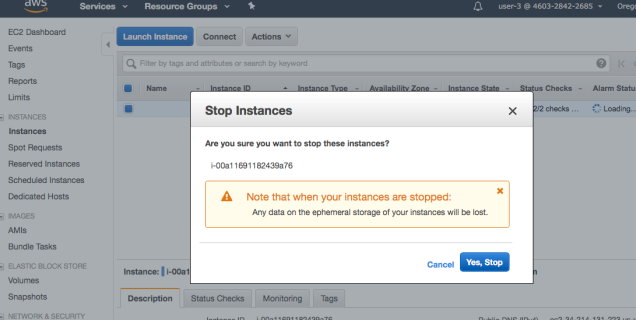
Click Yes, Please to perform the action. Yes !! Its working. Now you can see without any error message its started to stopping.
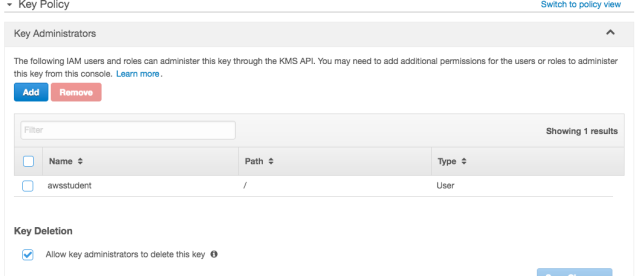
Cheers ! You have completed Introduction of Amazon IAM. Thank you for reading this and my next blog post will be Introduction to AWS key Management.
Drop me an email if you need any clarification about anything. You can find my details in About page
Stay Tuned !